I thought it was Surge that had that unfortunate side effect.
I thought it was Surge that had that unfortunate side effect.
If they arrest someone to gain access to their key, they don’t need this attack to use their key. They can just use their key.
One thing the article doesn’t make very clear is that for 2FA the PIN requirement comes from the site itself. If the site requires User Verification, the PIN is required. If not, it is not prompted even if set and this attack is possible. The response to the site just says they knew it.
It is different for Passkeys. They are stored on the device and physically locked behind the PIN, but this is just an attack on 2FA where the username and password are known. (In depth it’s more than that, but for most people walking around with a Yubikey…)
It also seems limited in scope to the targeted site and not that everything else protected by that specific Yubikey. That limits how useful this is in general, which is another reason it is sort of nation-state level or an extremely targeted attack. It’s not something your local law enforcement are going to use.
I think the YubiHSM is a much more appealing target, but that isn’t so much a consumer device and has its own authentication methods.
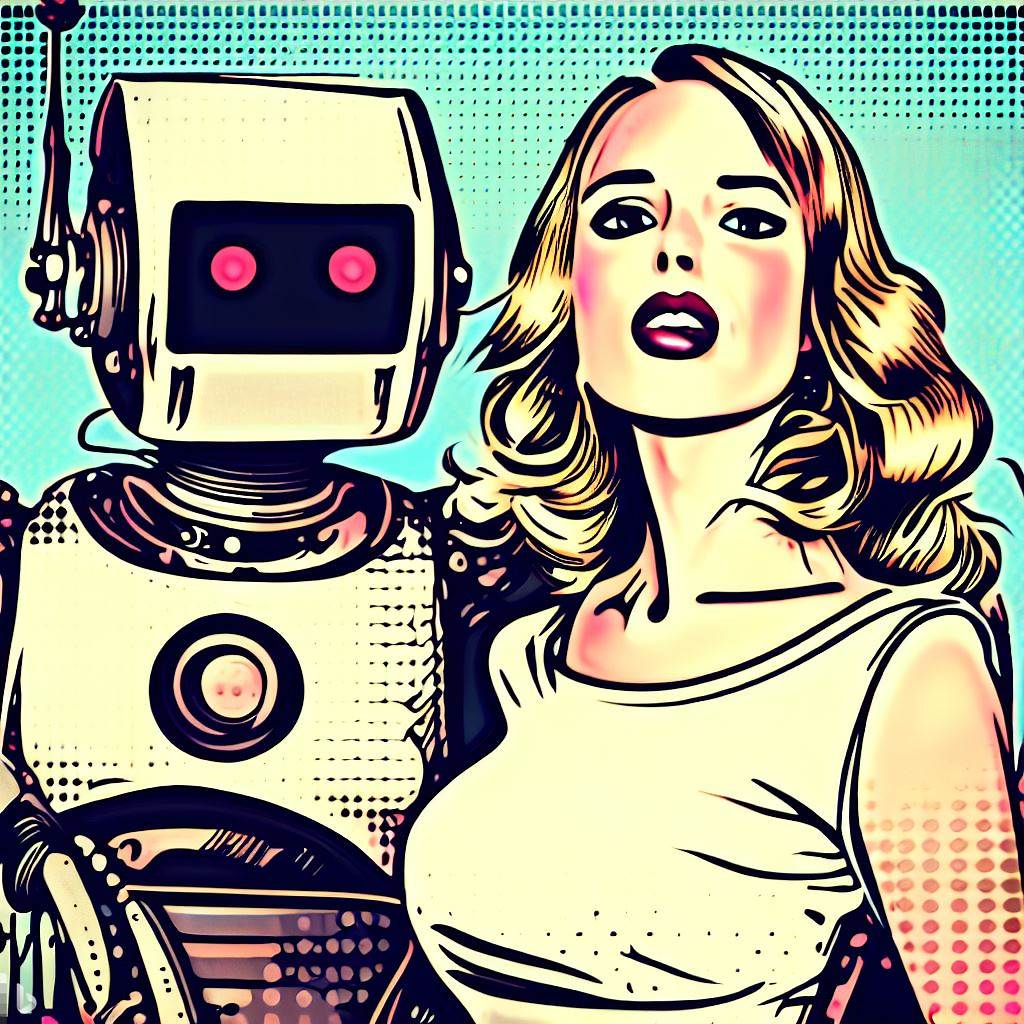
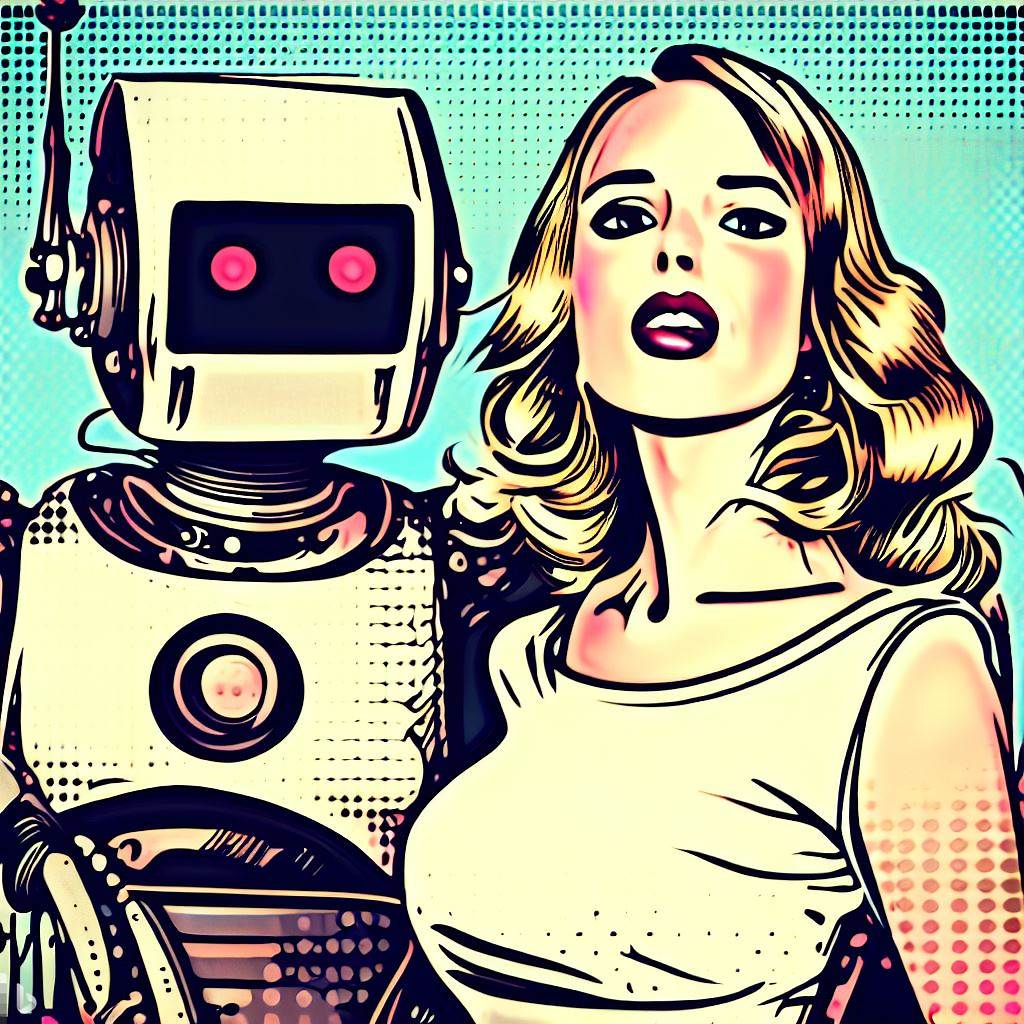
The bot demonstrated very well what this article is about. I don’t know the internals, but I also can’t image the bot was using the best and most expensive ways of doing analysis.
It was pretty bad at “getting the point” even when it was obvious, a better system should be able to do so. Sometimes the point is more difficult to discern and there has to be some judgement, you can see this in comments sometimes where people discuss what “the point” was and not just the data. I imagine an AI would have some difficulty determining what is worth summarizing in these situations especially.
Different applications have better performance on one vs other. Google Cloud still offers a lot of Nvidia options.
I was confused how a resume or application would be largely affected, but the article points out that software is often used to look over social media now as part of hiring (which is awful).
The bias when it determined guilt or considered consequences for a crime is concerning as more law enforcement agencies integrate black box algorithms into investigative work.
Amazon is notorious for combining stock, “the seller” often doesn’t matter.
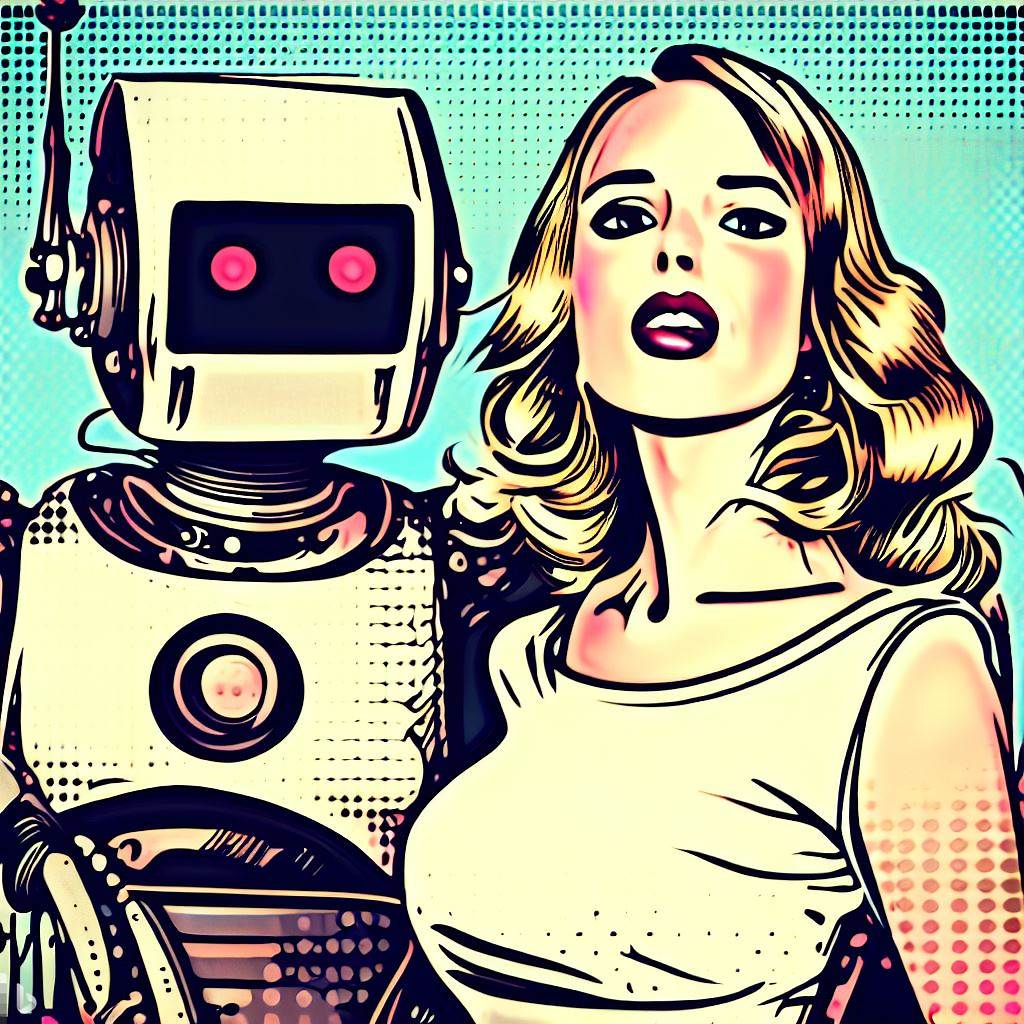
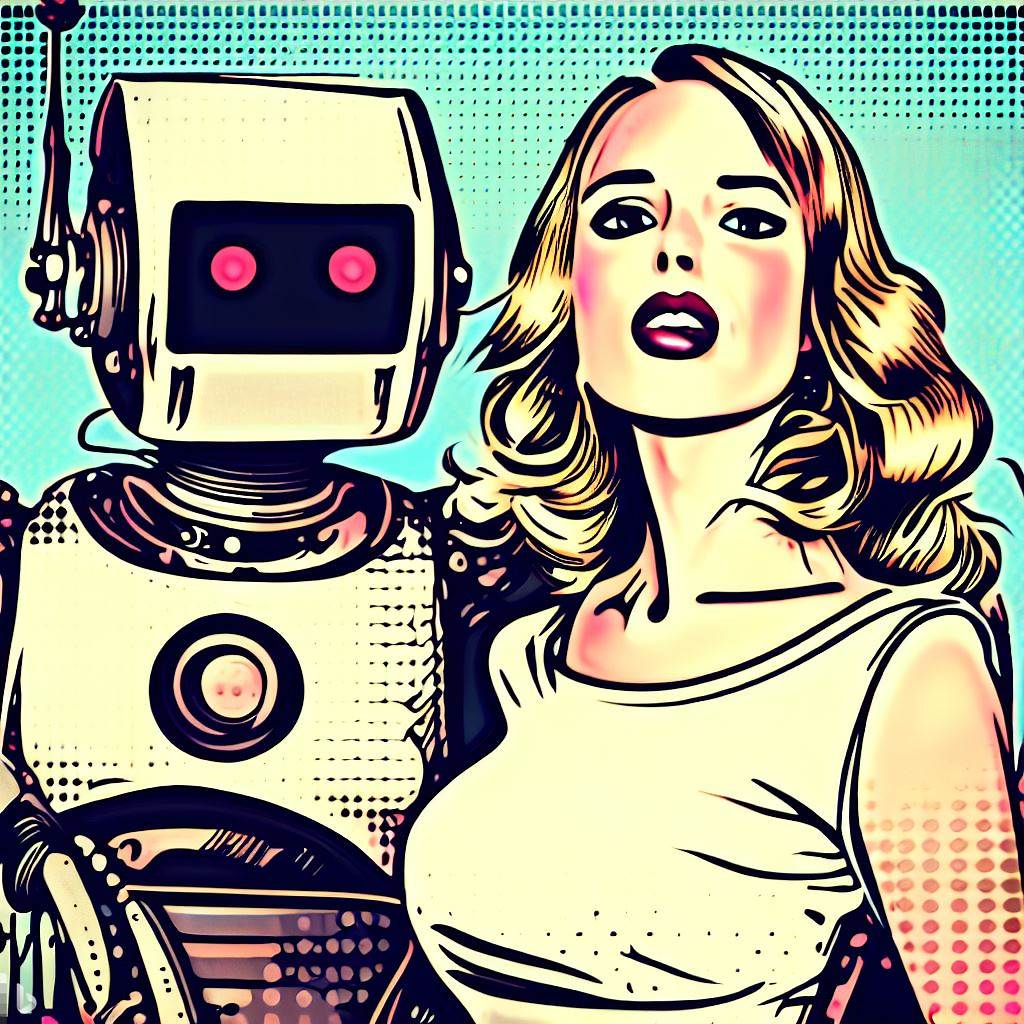
I think this is the crux of the article. In the past most people have considered photographic evidence to be very convincing. Sure, you could be removed from a photo of Stalin, and later people could do photoshop (with varying realism), now it’s a few words to make changes that many people believe without hesitation. Soon it will happen to video too, very soon.
Most people are not ready for it. Even shitty AI photos on social media get huge reactions with barely a handful calling them out.
Normal based on what? The ads exist because plenty of normal people use them to decide where to buy things or certain items. If they didn’t bring people in the stores wouldn’t bother.
Do you regularly use their ads to compare prices and select what to buy at each one, or generally stick to one place with a few trips to another one?
I think you explained it fine, it just doesn’t make sense to people who only go to the same place.
Difficult to fix if exploited.
Can be patched beforehand.
Sir, this is a Wendy’s.
It’s not just the title that is poorly written. The entire thing is written like “the sky is falling because memory chips and big computer stuff has a broken”.
According to them, “The threat intel data noted in this report is available to tens of thousands of customers, partners and prospects – and hundreds of thousands of users.”
It seems like they are trying to say their network is fine.
Amazon sold at a loss, but I don’t imagine the employees or suppliers and their employees feel like being paid was a waste.
How dare they not commission a piece.
Laptops are often taken outside the network.
Do xsnow and xpenguins next!
Harder on the corporate side, but this has been an issue in the warehouses.